VoicePlus Atrium — one platform managing mobiles, laptops, lifecycle, and Intune security under one roof
For years, Australian businesses have managed their mobile fleets through one set of tools and processes — and their laptops through another. Or worse, not managed their laptops at all. The result is fragmented visibility, duplicated effort, and security gaps that widen every time a device falls through the cracks.
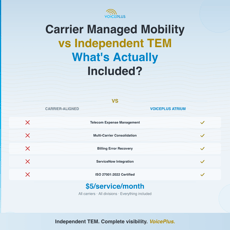
Carrier Managed Mobility vs Independent TEM — What's Actually Included?
If your organisation is evaluating managed mobility options, you've probably been presented with a carrier-aligned service that promises to handle your fleet end-to-end. On paper, it looks comprehensive. In practice, there are gaps that only become visible once you read the fine print — or once the invoices start arriving.
What Enterprise-Grade Mobility Governance Actually Looks Like
Managing a mobile fleet of a few hundred services is administration. Managing a fleet of several thousand across multiple carriers, divisions, and cost centres is governance — and the difference matters.
Why Employers Must Act on Emergency-Calling Risks | Triple Zero
Why Employers Must Act on Emergency-Calling Risks — Not Wait for Telcos For Australian organisations, emergency response is no longer just a telecommunications issue — it is a workplace safety, governance, and enterprise risk management obligation.
What Is A Device Refresh Program?
A device refresh program is a process in which an organisation periodically replaces its existing devices, such as smartphones, laptops, or tablets, with newer models. The purpose of a device refresh program is to ensure that employees have access to the latest technology and features, which can help improve their productivity and efficiency.
What Is Device Retrieval Program ?
A device retrieval program is a system or process in place for an organisation to retrieve their devices (such as smartphones, laptops, or tablets) from employees who are leaving the company or transferring to another department. This program helps to ensure that the organisation's sensitive data and intellectual property are protected and that the devices are returned in good working condition.
Spotting and Avoiding Common Telecom Billing Errors
Managing your business telecommunications expenses is a smart choice and essential for running your business smoothly. But a sneaky culprit often slips under the radar: billing errors. These tricky issues, which range from overcharges to misapplied rates, are more common in the telecom world than you might think. The catch? They're often buried in the complexities of telecom invoices, quietly chipping away at your resources.
4 Ways to Enhance Secure Employee Behaviour
The security of an organisation's data and information is of paramount importance. Achieving robust cybersecurity isn't solely dependent on advanced technology or sophisticated software; it begins with the employees' behaviour. Secure employee behaviour is the frontline defence against cyber threats.
Enhancing Mobile Security: Insights from Scamwatch Reports
Enhancing Mobile Security: Insights from Scamwatch Reports Mobile security has become a top concern for all of us. Scammers are constantly coming up with new tricks to target our mobile devices. The latestScamwatch reportsshow that Australians lost over $455 million to scams in 2023, with phishing being the top scam tactic.
How Vodafone's $5 Roaming Pack Revolutionises Inflight Mobile Use
Vodafone Australia just changed the game for travellers:introducing a $5 roaming pack, uniquely designed for international inflight use. This is a first for Australia, marking a major step in transforming how we connect above the clouds. Gone are the days of being disconnected while flying overseas.
- 1
- 2
3 Strategies to Reduce Telecom Cost