06 June 2021
App management
Newly available protected apps for Intune
The following protected apps are now available for Microsoft Intune:
- Leap Work for Intune by LeapXpert Limited
- iManage Work 10 For Intune by iManage, LLC
For more information about protected apps, see Microsoft Intune protected apps.
New tiles provided app install failure count
The Home, Dashboard, and Apps Overview panes now provide updated tiles to show the number of app installation failures for the tenant. In the Microsoft Endpoint Manager admin center, select Home to view the Home pane, or Dashboard to view the Dashboard pane. Select Apps > Overview to view the Apps Overview pane. For related information, see Intune reports.
Device configuration
Per setting status report in Settings Catalog
When you create a Settings Catalog profile, you can see how many devices are in each state, including success, conflict, and error (Devices > Configuration profiles > select the policy). This report includes a Per setting status that:
- Shows the total number of devices impacted by a specific setting.
- Has controls to search, sort, filter, export, and go to the next/previous pages.
For more information on the settings catalog, see Use the settings catalog to configure settings on Windows and macOS devices.
New settings for iOS/iPadOS 14.5 devices and newer
When creating a device restrictions policy for iOS/iPadOS devices, there are new settings available (Devices > Configuration profiles > Create profile > iOS/iPadOS for platform > Device restrictions for profile):
- Block Apple Watch auto unlock: Set to Yes to block users from unlocking their device with Apple Watch.
- Allow users to boot devices into recovery mode with unpaired devices: Set to Yes to allow users to boot their device into recovery with an unpaired device.
- Block Siri for dictation: Set to Yes to disable connections to Siri servers so that users can't use Siri to dictate text.
- Require devices to use Wi-Fi networks set up via configuration profiles: Set to Yes to require devices to only use Wi-Fi networks set up through configuration profiles.
To see these settings, go to iOS and iPadOS device settings to allow or restrict features using Intune.
Applies to:
- iOS/iPadOS 14.5 and newer
Device management
Support has ended for Restart remote action on Android Enterprise corporate-owned devices with a work profile
Support has ended for the Restart remote action on corporate-owned devices with a work profile. The Restart button has been removed from the Device page for corporate-owned devices with a work profile. If you try to restart devices using bulk device actions, the corporate-owned work profile devices won't restart and those device actions will be marked report as Not supported. Other device types that are included in the bulk device action will restart as normal for that action.
Windows 10 Enterprise multi-session support (public preview)
Windows 10 Enterprise multi-session is a new Remote Desktop Session Host exclusive to Windows Virtual Desktop on Azure which allows multiple concurrent user sessions. This gives users a familiar Windows 10 experience while IT can benefit from the cost advantages of multi-session and use existing per-user Microsoft 365 licensing.
Microsoft Intune lets you manage multi-session remote desktops with device-based configurations like a shared, user-less Windows 10 client. You can now enroll Hybrid Azure AD joined VMs in Intune automatically and target with OS scope policies and apps.
You can:
- Host multiple concurrent user sessions using the Windows 10 Enterprise multi-session SKU exclusive to Windows Virtual Desktop on Azure.
- Manage multi-session remote desktops with device-based configurations like a shared, user-less Windows 10 Enterprise client.
- Automatically enroll Hybrid Azure AD joined virtual machines in Intune and target them with device scope policies and apps.
For more information, see Windows 10 Enterprise multi-session remote desktops.
Device security
Conditional access on Jamf-managed macOS devices for Government Cloud now available
You can now use Intune's compliance engine to evaluate Jamf-managed macOS devices for Government Cloud. To do so, activate the compliance connector for Jamf. For more information, see Integrate Jamf Pro with Intune for compliance.
Changes for the Microsoft Tunnel Gateway
We have a pair of updates to announce for the Microsoft Tunnel Gateway this month:
-
Microsoft Tunnel Gateway is now generally available
With this service release, Microsoft Tunnel Gateway is now out of preview, and generally available. While the Microsoft Tunnel Gateway server component is out of preview, the following Microsoft Tunnel client apps remain in preview:- Microsoft Tunnel standalone app for Android
- Microsoft Tunnel standalone app for iOS
- Microsoft Defender for Endpoint with support for Microsoft Tunnel for Android
-
Custom setting support in VPN profiles for Microsoft Tunnel for Microsoft Defender for Endpoint for Android
When you use the Microsoft Defender for Endpoint as your Microsoft Tunnel client app for Android and as a mobile threat defense (MTD) app, you can now use custom settings in the VPN Profile for Microsoft Tunnel to configure Microsoft Defender for Endpoint.
In this scenario, using custom settings to configure Microsoft Defender for Endpoint in the VPN profile removes the need to deploy a separate app configuration profile for Microsoft Defender for Endpoint.
For the following platforms, you can choose to use either the custom settings in the VPN profile or to use a separate app configuration profile for Microsoft Defender for Endpoint:
- Android Enterprise Fully Managed
- Android Enterprise Corporate-Owned Work Profile
However, for Android Enterprise Personally-Owned Work profile, use only the VPN profile with custom settings. Personally-Owned Work Profile devices that receive a separate app configuration profile for Microsoft Defender for Endpoint in addition to a Microsoft Tunnel VPN profile may be unable to connect to the Microsoft Tunnel.
Monitor and troubleshoot
New operational report providing app install status
The new App Install Status report provides a list of apps with versions and installation details. App installation details are included as separate columns in the list. Additionally, the installation details provide the app install and failure totals for devices and users. You have the ability to sort and search this report as well. In the Microsoft Endpoint Manager admin center, select Apps > Monitor > App Install Status. For more information about reports in Intune, see Intune reports.
New operational report providing app install status based on device
Based on a selected app, the new Device Install Status report provides a list of devices and status information related to the specific app. App installation details related to the device includes UPN, Platform, Version, Status, Status details, and Last check-in. You have the ability to sort, filter, and search this report as well. In the Microsoft Endpoint Manager admin center, select Apps > All Apps > Select an app > Device Install status. After selecting an app, click Generate report. For more information about reports in Intune, see Intune reports.
New operational report providing app install status based on user
Based on a selected app, the new User Install Status report provides a list of users and status information related to the specific app. App installation details related to the user include Name, UPN, Failures, Installs, Pending, Not Installed, and Not Applicable. You have the ability to sort, filter, and search this report as well. In the Microsoft Endpoint Manager admin center, select Apps > All apps > Select an app > User Install Status. After selecting an app, click Generate report. For more information about reports in Intune, see Intune reports.
Export Intune reports using Graph API v1.0 or beta
Intune reporting export API now is available in Graph v1.0, and continues to be available in Graph beta. For related information, see Intune reports and Export Intune reports using Graph APIs.
Scripts
New property value supported for Android Open Source Project devices
The IntuneAosp property value is now supported in the managementAgentType enum. The ManagementAgentTypeID value for this property is 2048. It represents the device type that is managed by Intune's MDM for AOSP (Android Open Source Project) devices. For related information, see managementAgentType in the beta section of the Intune Data Warehouse API.
Week of May 10, 2021
App management
Improved Conditional Access messaging for Android and iOS/iPadOS users
Azure Active Directory has updated the wording on a Conditional Access screen to better explain access and setup requirements to users. Android and iOS/iPadOS users will see this screen when they try to access corporate resources from a device that's not enrolled in Intune management. For more information about this change, see What's new in Azure Active Directory.
Device security
Windows Security experience profiles support tri-state settings
For Windows 10 devices, we’ve updated the bi-state settings to be tri-state settings in the Windows Security experience profile for Endpoint security Antivirus policy.
Most settings in the profile previously supported only two options of Yes and Not configured. Moving forward, those same settings now include Yes, Not configured, and a new option of No.
- For existing profiles, settings that are set to Not configured remain as Not configured. When you create new profiles or edit an existing profile, you can now choose to explicitly specify No.
In addition, the following applies to configuration of the setting Hide the Virus and threat protection area in the Windows Security app and its child setting Hide the Ransomware data recovery option in the Windows Security app:
- If the parent setting (Hide the Virus and threat protection area) was set to Not configured and the child setting was set to Yes, both the parent and child settings will be set to Not configured.
Device management
Use filters to assign policies in Endpoint Manager admin center - public preview
There's a new Filters option that can be used when assigning apps or policies to groups. To create a filter, go to:
- Devices > Filters (preview) > Create
- Apps > Filters (preview)> Create
- Tenant administration > Filters (preview)> Create
You can filter the scope of affected devices using device properties. For example, you can filter on the OS version, device manufacturer, and more. After you create the filter, you can use the filter when you assign a policy or profile.
For more information, see Use filters (preview) when assigning your apps, policies, and profiles in Microsoft Endpoint Manager.
Applies to:
- Android device administrator
- Android Enterprise
- iOS/iPadOS
- macOS
- Windows 10 and newer
Use Intune policy to expedite installation of Windows 10 security updates
In public preview, you can use Intune’s Windows 10 quality updates policy to expedite the install of the most recent Windows 10 security updates to devices you manage with Intune.
When you expedite an update, devices can start the download and install of the update as soon as possible, without having to wait for the device to check in for updates. Other than expediting the install of the update, use of this policy leaves your existing update deployment policies and processes untouched.
To help monitor expedited updates, you can use the following options:
- The Windows Expedited Updates report
- Expedited update failures device report
Latest from the Blog
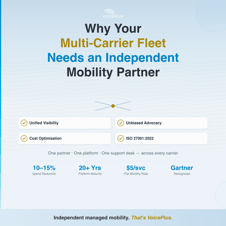
3 Strategies to Reduce Telecom Cost